Welcome to part 2 of my journey into cyber security. So, what now? What have I been learning since the last post?
Well oddly enough, this article discusses something a bit more fundamental. Rather than going over all the sexy/dry details of what a penetration tester is and does, I have found myself coming to reflect on what my learning approach has been like up to now. Previously, I would pick a role, find relevant certs and then study towards it.
So let’s break this down:
The Initial Approach
- I would think about what I would like to do as a role. Let’s say be a network technician.
- I would look up which certifications are in demand and settle on something that seems popular. In this case let’s say Cisco CCNA Routing and Switching.
- I then go off and find study material on the subject (books, Packet Tracer, Boson practice exams) and enrol in a course. Hell I even buy some kit from eBay to setup my home lab.
- I then spend nine months studying this certification while working full time, aiming to put in between ten and sixteen hours a week, depending on my schedule.
Sounds reasonable right? You hear about all these guys who can ace it in three months, maybe a little more. Surely I could make this work for me too right?
Wrong.
I’m going to tell you why everything above didn’t work. Then I’m going to tell you what I’m going to do to change my approach, and how I believe this will prepare me for achieving my career goal of becoming a penetration tester. In other words, I am going to teach myself how to learn again.
Let’s highlight what happened after the nine months I spent studying a CCNA;
The Ambition
- I had a book by Todd Lammle that was good, but apparently didn’t meet the requirements of the later version of the exams at the time. So I felt I had to buy new books. I ultimately went with the Wendell Odum series, as it was recommended by Cisco directly. The material is over twice the length of the Lammle book, causing my study time to stretch out even more.
- The Cisco academy site proved useful and Packet Tracer even more so. However this made me realize all that kit I bought off eBay was kind of redundant to an extent. Not to mention the fact that running the things in the living room while my partner tried to watch TV was just a bit of a no no. Presently they sit on my shelf gathering dust.
- The course I enrolled on had great learning material online, complete with labs. The classroom experience on the other hand was in a dingy, tired looking computer science classroom in a low tier university somewhere. Despite the instructors best efforts, we as a class were typically held back by the weakest in the group. There were also module exams that although challenging, were nothing like the real exam. Ultimately I pulled out of the classes and focused on the online counterpart instead.
- When taking the Boson tests, I couldn’t really score anything above 54%. I made a point of not memorizing the questions and answers, taking the exam sparingly every few months.
Overall I gained nothing. No cert and thousands of pounds wasted in unfinished courses and half used material. What’s worse is that this isn’t the first time this has happened to me in my career in IT. So let’s go over what my mistakes were up to this point:
Mistakes Made
- I didn’t think about what the role I wanted to do really involved. Sure I looked up job descriptions on Linkedin and other career sites, but I didn’t actually understand what their day to day tasks were in detail. I didn’t approach existing professionals asking about their roles.
- I chose a certification based on its popularity within the industry. What I should have done was consider first of all, how could I directly apply what I learn? I realized that the company I worked for at the time didn’t use Cisco. The company I work for now (at the time of writing) doesn’t use Cisco. So why on Earth am I trying to learn about a technology I can’t use outside of a lab environment? I should have looked at the network technology they were currently using and learn that instead.
- I bought all the study material and the course, which didn’t seem like a bad idea. However, had I taken a bit more time to look at what they all offered, I could have avoided buying the Cisco kit and just used the virtual lab software Packet Tracer. I shouldn’t have walked away from the class based course, but rather use it differently. Sure it was frustrating rehashing material from the week before, but the module tests weren’t there to teach me how to pass the exam, but how to use my knowledge effectively in a real work environment. I should have used the lecturer more effectively.
- I didn’t book the real exam in advance. Therefore there was no real commitment, beyond what the class demanded of me. Therefore the focus wasn’t truly there.
- Most off all, I wasn’t allowing myself to fail. My ego was subconsciously trying to shield me from this throughout the whole thing. This meant missing out on learning opportunities. It was also free license to procrastinate as much as possible, even if it meant being ‘busy’.
Going Forward
With that now in consideration, let’s come back to the main point. How am I going to learn to become a penetration tester more effectively? Rather than repeat the whole process above, I decided I needed to take a step back and review.
It was during my academic ‘convalescence’ I came across a book that had something of an interesting premise. It was called Ultralearning by Scott Young. Now I’m a little cynical of self-help gurus as the next sceptic (still read them though), but this seemed a little different. What Scot advocates is the idea of refining your learning ability so as to assimilate knowledge or develop a new skill in the most focused, immersive and efficient way possible.
Now we’re not going to rehash this guy’s entire work in this post, but what I do want to do is tell you how I am going to use this to improve my learning approach.
The principals of which can be broken down as follows:
1: Metalearning
I have tasked myself with the goal of becoming a penetration tester. Sounds straight forward doesn’t it? Except what does a penetration tester actually do? What type of penetration tester do I want to be? Why does it interest me? Finally, how do I become one?
One of the first things Ultralearning encourages you to do is to research your chosen skill, spending 5-10% of your overall projected learning time devoted just to analysing your chosen topic. This includes answering the above mentioned question and seeking out experts who are already doing it. In addition you will want to break down what you intend to learn into facts, concepts and procedures. This will help you determine the best way to spend your time or approach to learning. This can be achieved by benchmarking against existing requirements, say through a job spec, degree curriculum, certification syllabus etc. Eventually you will begin to understand what you need to emphasize in your study and what can be excluded.
2: Focus
Procrastination and distractions; the dynamic duo of unfulfilled potential. Like many of you reading this, we get waylaid by distractions and make excuses not to do things. But what’s even more insidious is when we use legitimate activities as reason not to get things done.
From Scott’s book, I realized that a technique I had used during my Cisco studies to help me remain focused for short bursts at a time actually had a name. It’s called the Pomodoro Technique. For me, all I did was set a time for twenty fives to study. I then take a 5 minute break, before repeating the cycle again. Simple, effective, easy to implement.
However there were other factors to consider. For one, studying at home (at the time of writing this) has proven to be challenging during the week, especially having a full time job. Your environment is key to helping you focus. It used to be that in a previous job I would use their in house library. Then in my later job the local library. Unfortunately Croydon’s library can sometimes attract somewhat cacophonous characters to say the least…
Being in a one bedroom flat with cats and a partner can lead to disruptive distraction, essentially ruining the quality of one’s work. This isn’t their fault, but rather mine. So, going forward I have opted to study at home on the days my partner works, which happens to be the weekends. That’s about sixteen hours plus in a week where I can effectively study without interruption or feeling a guilty obligation to interact. It also frees me up during the week to be a more attentive boyfriend. I feel this is the best compromise I can do for now, as unlike some of the case studies Scott uses in his book, I don’t have three months or a year to take out to pursue my goal.
Final things to consider are the way you approach tasks and how your mind copes in this focused state. Some tasks will be harder to learn than others. In this respect you may have to try some different approaches in order to find the one that best helps you focus. Also, being a Human, your mind will inevitably have moments of turmoil. Scott likens the ability to focus to being something like a muscle. The more you train yourself to resist an urge to indulge a distraction, the easier it becomes to resist over time.
3: Directness
This was surprisingly simple and obvious, yet was clearly something I wasn’t doing in my earlier forays. Ultralearning present the problem of transfer, which from what I understand, means when you have trouble applying what you have learned in theory to direct practice. For example I could have a strong understanding of TCP/IP network fundamentals, yet have no idea how to configure a physical multi-layer switch.
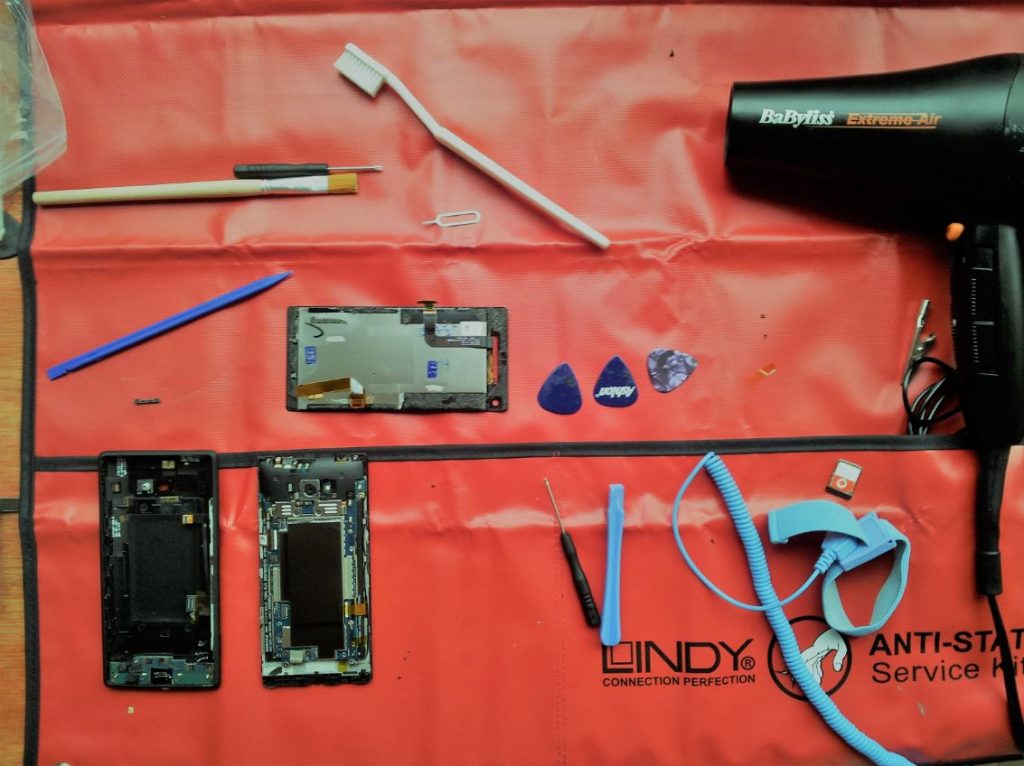
Scott advocates learning straight from the source, using multiple tactics such as project based and immersive learning among others. It’s not enough for me to know the theory behind penetration testing I need to be physically using it. This can be achieve through capture the flag games (CTF), building deliberately vulnerable lab environments to tinker with, or (perversely) try to fix and harden your workplace infrastructure based upon vulnerabilities you would have found. It’s not enough to simply learn the basics. You need to dig deep and research around the core premise as well.
4: Drill
Skills n’ drills. The aim is to focus on areas of my learning that can be broken now into isolated, repeatable tasks. This may not be as straight forward as it sounds. For one, the drill has to be directly applicable to the work I do. I mean sure, I can learn a dance to pass an exam, but it’s got to be useful beyond that right? Also the types of drills that need to be developed need to start with the areas I’m weakest in first. The Ultralearning book suggests using tactics such as ‘time slicing’ or ‘prerequisite chaining’. I’m not going to outline them all in detail, but the general gist is to analyse the sequence of actions or concepts that need to be learned and ensure you focus on them specifically, before integrating them back into the larger topic at hand. For example when understanding network concepts, it may be worth me spending more time drilling subnet calculations, rather than just trying to memorise general address ranges for the sake of classification.
5: Retrieval
Basically trying to remember what you learn. But the trick here is to ensure you get into the practice of doing it without having to constantly compare to a reference point. Namely because you want to understand the framework used to find the answer, rather than just learning the Q&A sequence itself. In effect Scott Young tries to move you away from simply reviewing the material. Methods towards improving retrieval include using flash cards, self-generated challenges and freely recalling details straight after studying (no peeking at the material though). I did experiment with this to some extent when studying for and passing my Network+ exam. I created my own questionnaires, built micro networks in packet tracer and attempted to use some mnemonics (see retention below) to mentally recall data.
6: Feedback
This one was a little more tricky for me, not just because I have a little bit of an ego but namely because I often work alone. The book does point out that feedback can serve to be of little value if it does not critically and suitably deconstruct the outcome of your work. I recall taking a City & Guilds Cyber Security EPQ (its first iteration no less) course and passing the exam. However I was unhappy with the absence of feedback. Despite chasing it up, there was no information provided on what I did right or wrong. I effectively learned nothing from my endeavour. However, feedback can come to me in the form of a tutor or perhaps even peers. I found the worst feedback came from people close to me, my friends and my family. It feels harsh saying it, but they are seldom going to tell you things as they really are. In some cases they may not be even qualified to assess your work at all.
When seeking feedback, Scott suggests finding what he calls a difficulty sweet spot. Where there is enough challenge to make you think without defeating you. While also ensuring your success doesn’t lull you into a false sense of certainty. Another thing I took from it was the concept of diminishing returns. If my approach to learning of a topic has dragged to a crawl, then it is time to find and try a different approach.
7: Retention
Scott Young goes into a few discussion about the nature of memory and how it works. This can range from learning and forgetting things through time, overwriting data with new or what is described as a locked box with no key (think of when you had something on the tip of your tongue, but could not recall). Regardless of what you believe is the case, he goes on to suggest trying a few things. These include proceduralization (effectively turning something into a repeatable habit), overlearning (practicing at a level above your ability), repetition and mnemonics.
Now I have previously already repetition and mnemonics through the use of self-created questionnaires and association diagrams. I found the former to be pretty effective for learning things like network port numbers and their associated protocol. The latter I had mixed success with. I unfortunately have a fairly literal mind, which makes using strange image and wording to remember key concepts a little challenging. It could also explain how I can figure someone’s degree subject out by looking at their library, yet can’t even solve basic riddles. This is of slight concern, as doing well in cyber security does require a certain degree of lateral thinking. Still, overlearning does seem to be a new concept to me and will likely be something I need to incorporate into my studies. Doing more riddles probably wouldn’t hurt either.
8: Intuition
This one isn’t so much a technique but rather developing a mindset. Scott also seemed to wax lyrical about how Richard Feynman’s approach to solving problems could in some ways be replicated, despite the fact the man possessed an almost singular level of intellect. The main things I took from this section was that I shouldn’t give up on challenging problems too quickly, prove that I understand the concept thoroughly and start with solid examples. What I also want to avoid doing is simply summarizing complex concepts when learning them, as I may end up skipping over important details. I took the previously mentioned approaches when learning about subnetting. I book a book that specialized in the topic specifically and just went through each concept over and over again, making sure I knew how the binary calculations worked and understanding the pattern that was involved. It was not fun or sexy, but it did make doing the questions in the exam a lot simpler to complete.
9: Experimentation
This was not what I expected. What I needed to do really was learn the rules form people who make them work well. From there I have a foundation. But after this, it apparently becomes increasingly difficult to find resources to teach yourself more advanced concepts. Thus I will need to experiment with different techniques, resources and styles in order to progress and grow.
I don’t think I’m quite at a level to be innovating in this field, but I can certainly copy and create new tools and approaches from the considerable resources that are already out there. An interesting suggestion includes learning and combining unrelated skills. For example I could learn the Russian language and C++ to create a Cyrillic password cracking app. Or perhaps an abusive chatbot with a surprisingly inventive vocabulary.
So now that I’ve broken down how I intend to use this Ultralearning approach, what do I do going forward? Oddly enough I’ve chosen to use this approach with the AZ-500 certification I am currently in the middle of. I took a step back and researched the topic a little more thoroughly, building a mind map of how I want to approach the exam. This included breaking the syllabus requirements down into facts, concepts and repeatable procedures. It meant linking my research to the source, in this case Microsoft Docs. I also created a separate section for projects and other direct application opportunities for what I was learning. It wasn’t enough to simply pass, but to actually make what I have learned useful and applicable in my career.
If I can make it work for this, then I can at least be better prepared for the tasks needed to become a penetration tester. I have unique challenges ahead of me, especially as I do not have a more traditional computer science academic background. But if I can apply this new sense of focus and method to learning, then there really shouldn’t be anything to stop me.
Pingback: My Journey Into Cyber Security Part 3 - adrianjfletcher.com