The Journey Continues
You came back for another huh? Or maybe this is the first post you have seen on my site. Either way, my path to becoming a cyber security professional continues. Today we’re going to cover the operating system Linux.
So what is Linux? Well for one, it’s not Windows. Now that we have that out of the way, let’s give you a brief overview:
- Linux is a Unix like family of operating systems (OS) based upon a Linux kernel, first developed by Linus Torvalds (Linus + Unix = Linux, geddit?) in 1991. You can read up on its history by clicking here.
- It has since grown to become one of the largest open source, collaborative software projects in the world. It powers the majority of the world’s cloud infrastructure and the majority of Android phones run off a subset of Linux.
Why Learn Linux?
Why am I writing about this today? To be honest it’s one of the foundation skills I would need, in order to be able to conduct any kind of cyber security work. As explained previously, a great many web servers and network infrastructure runs on Linux (including this website).
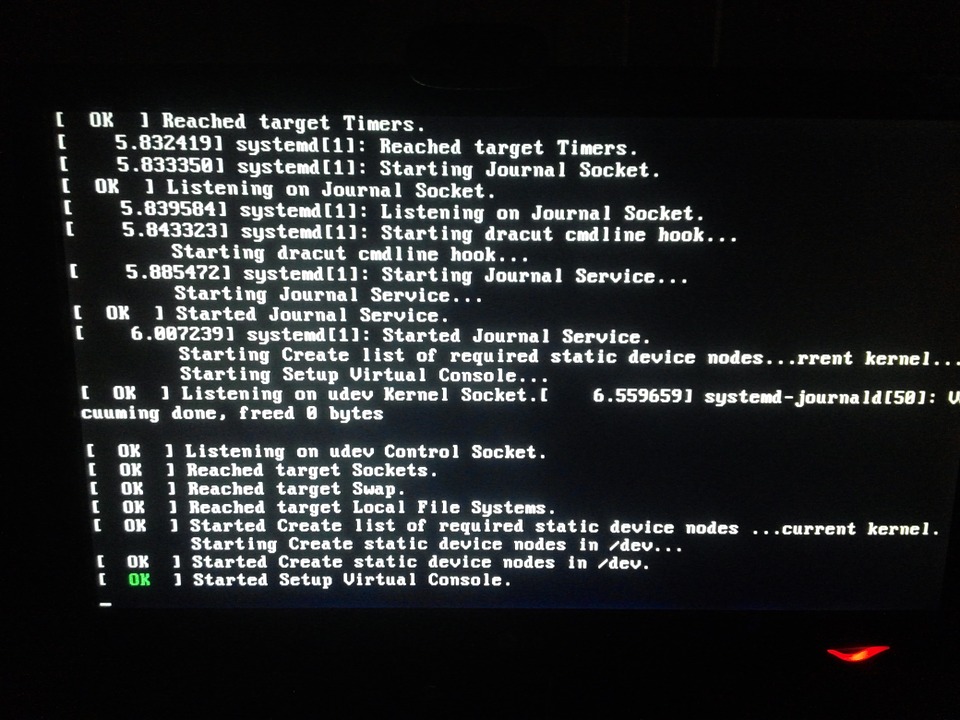
A lot of tools used by cyber security professionals are designed to run in Linux. Also being free for the most part, I can create multiple test environments at little expense to myself. Now that’s not to say all Linux distributions (known as distros) are suitable for rookies like you and me. Arch Linux for example is not really suitable for complete beginners, due to the fact you have to compile a great deal of it yourself. In a sense, it’s the kit car of Linux distros. Then there is Ubuntu, which I’m currently using. It’s pre-built, comes with a load of existing tools and can be installed fairly easily. Most of all, there’s a great deal of forums and guides on how to use and troubleshoot it.
Learning by Doing
To teach myself how to use Linux effectively, I have both watched videos and taken notes from Alex Ahmed’s Hackersploit Linux Essentials series, as well worked on little Linux home projects. I chose Hackersploit over other videos simply because Alexis cuts out a lot of the filler. He says so himself in that he takes an almost Pareto 80:20 principal when teaching about Linux. As such you learn mostly about file directory navigation and manipulation, setting permissions, configuring firewalls and SSH among other things. You don’t get long history lessons or in depth analysis on disk volume partitioning.
At this point in time I have used what I have learned to build the server running this site, create DNS servers for redirecting pop up ads and desktop alternatives to WIndows. Nothing too clever and often using a Raspberry Pi or virtual machine. I am now eying up some more projects to work on, though they will be covered in separate blog posts. The main thing I want to take from Hackersploit is having the bear minimum tools to do some low tier cyber security challenges.
An example of such a challenge are the CTF exercises found at picoctf.org. Admittedly this site is intended for American school children, it is however a capture the flag (CTF) type game. Written by security experts at Carnegie Mellon University, it gives you the opportunity to explore a variety of different CTF games involving hacking, reverse engineering, cryptography and others. I managed to solve most of the ‘General Skills’ challenges just with the Linux Essentials course alone, though I had to teach myself a little bit about a tool called NetCat along the way.
Conclusion
So far it seems I am slowly getting through the Linux tutorials, having already put them to some use. I will need to keep practicing. The OverTheWIre Wargames site is a good way to learn about using basic Linux commands. I’ve resisted looking at the walkthroughs on these so far. I’ll probably publish details on my progress with this, once I’ve made time to go through some of them.
Another thing that has come up in my research is the concept of bug bounty hunting. In principal, this is when hackers join up with bounty programs and within a given scope, hack client websites and applications, searching for flaws and vulnerabilities. Depending on whether they’re the first to find it, they then get paid a bounty (normally cash). The amount varies depending on severity, but what made this opportunity uniquely interesting is that don’t need to be employed with a specific firm to carry this out.
Now I have to be careful, as it’s all too easy to drift off down different rabbit holes. I still need to map out the research needed to do the OSCP, but admittedly that course is geared towards infrastructure hacks, not web. I guess I have a fair bit to reflect on at this point.
Until next time.
Pingback: My Journey into Cyber Security Part 5 - adrianjfletcher.com Adrian Fletcher